























SecureXserverless|relay|modules?... Right. What?!
Yes! SecureX serverless relay modules integrate third-party systems into SecureX. This tool enables SecureXThreat Response toobserve, deliberate, refer, and respond to observables from third-party solutions. What does this all mean? Read on, You'll find out in this blog post. And you can learn more, and ask questions, at ourupcoming webinar on April 13th.
You can even do a guided workshop of thenew DevNet learning module. It willteach you how to integrate the not-yet-integrated!
For most, I won't have to explain why it is of great importance to integrate as many sources of information as possible into a security platform like SecureX. It is very important nowadays to stay up to date with all of the cyber threats that are posing all over the world. It is widely known that there are not enough resources to be found to fill up every Security Operation Center (SOC).
Therefore, many organizations struggle with coping with the massive amount of new types of attacks and generated alerts from their tooling. This is where SecureX, and integrations with SecureX come in to play: now your incident responders can levarage a single tool, SecureX, to respond to potential threats. This saves time, and also many errors.
There are a couple of ways to do this. First, let me explain a little bit about Cisco Threat Intelligence Model (CTIM).
For SecureX, CTIM is the data model -an abstract model that organizes data and defines data relationships. CTIM is of utmost importance for SecureX because it provides a common representation of threat information, regardless of whether its source is Cisco or a third party. Think of each of these processes as part of a data refining pipeline. The data refining pipeline gathers raw data, such as information about how computer software behaves in a variety of contexts. It then progressively refines that data by decomposing and structuring it, enriching it by placing it in context with data from other origins, with its own varying levels of refinement. Refining it in this way enables us to isolate the parts of the data that we can use for informed decisions. The end result is what we call actionable intelligence. This is what SecureX offers to its users to act quickly and without errors.
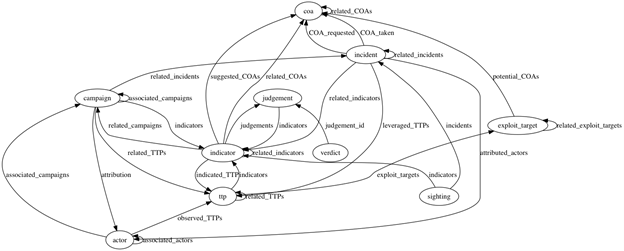 Cisco Threat Intelligence Model (CTIM)
Cisco Threat Intelligence Model (CTIM)
Now back to the integration methods. There are basically three methods:
The serverless relay can be deployed anywhere: on the application, on bare metal server, on VM, or in cloud-based systems such as AWS Lambda, Azure Functions, or Google Cloud Functions. In the earlier mentioned DevNet learning module, we will deploy the serverless relay module in AWS. The function of this relayis to translate between CTIM and whatever the third-party solution "speaks." This makes it possible for a third-party solution to insert valuabledata into SecureX, which can be leveraged to create actionable intelligence. Also, SecureX is able to give certain response actions back to that third-party solution for remediation.
We will talk more about theSecureX serverless relay moduleslearning lab, and how it will help you learn this yourself, at the April 13th webinar.For now, know that when you complete the learning labs, you will have learned:
Register for the April 13th webinar
There are also several Cisco Live 2021 sessions that talk about this (e.g. DLBLDR-11, BRKSEC-2005, BRKDEV-2010 and HOLSEC-3003).
A big thank you to Brennan Buchard, Ed McNicholas, H?kan Nohre, Ian Gyte, Oxana Sannikova, and Patrick Cardot for creating this awesome content together!
We'd love to hear what you think. Ask a question or leave a comment below.
And stay connected with Cisco DevNet on social!
Twitter @CiscoDevNet | Facebook | LinkedIn
Visit the new Developer Video Channel
 Горячие метки:
Cisco DevNet
Cisco SecureX
Security Operations Center (SOC)
Горячие метки:
Cisco DevNet
Cisco SecureX
Security Operations Center (SOC)